Posts
We continue the cycle and now let’s talk about another “relative” of SAST and DAST - IAST…
October 18, 2025 at 7:54 PM•Max Knyazev is typing…Telegram mirror
We continue the cycle and now let’s talk about another “relative”
SAST
and
DAST
—IAST
🥳
What is IAST?
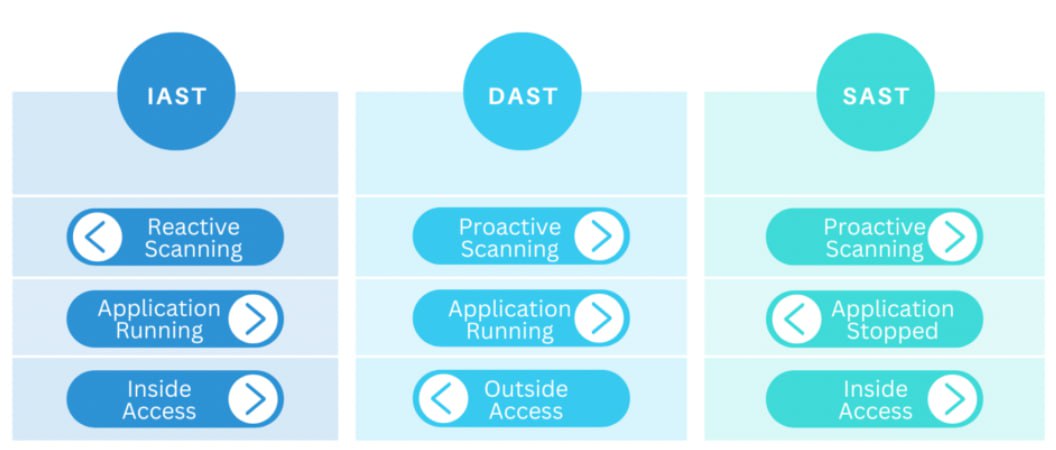
IAST stands for Interactive Application Security Testing. While SAST works with code and DAST looks at the application from the outside, IAST combines both approaches and works from the inside out. This is an agent that is embedded directly into a running system and analyzes everything that happens: from code processing and requests to application behavior in real time
⏱
What is IAST used for?
IAST is needed to identify vulnerabilities as accurately as possible and minimize the number of false positives. Imagine you have a complex web application. The IAST scanner connects to it like a regular user, but at the same time monitors from the inside how the application works: what data passes through the methods, what happens with queries to the database, how parameters are processed, etc. That is, if DAST sees that “something went wrong,” then IAST can immediately highlight a specific section of code or library in which there is a problem
😎
How does it work?
IAST is injected into an application while it is running, typically through a special agent that runs with the application. The agent analyzes code execution in real time: intercepts function calls, watches how data travels from the user to the database and back. As a result, we get a combination: the accuracy of static analysis + the practicality of dynamic
👍
This is convenient at least because IAST doesn’t just say “you have XSS”, but shows “here, in such and such a line of code, when entering a parameter, the call went to such and such a function, and it was this function that opened the hole.” This is a huge plus for developers, because they don’t have to guess where exactly to dig
🧰
How to use IAST?
Usually IAST is installed on a test environment, but sometimes it is also installed on “production” servers - in order to catch problems directly in real traffic ( although there are nuances regarding performance and security ). Integration can be with CI/CD or during QA testing
👍
Tools for Implementing IAST
There is almost no pure open source under IAST ( unlike SAST/DAST ). These are mainly commercial solutions. Among Western instruments - Contrast Security, Seeker. Russian players - PT Application Inspector ( IAST is built into the tool ) and Solar appScreener ( it also knows hybrid analysis modes )
🤩
I hope the picture now lines up better: SAST looks at the code, DAST looks at the application from the outside, and IAST combines and looks directly from the inside. Next time we’ll talk about another interesting class of solutions
😎
#information_security #iast
Open original post on TelegramWhat is IAST?
IAST stands for Interactive Application Security Testing. While SAST works with code and DAST looks at the application from the outside, IAST combines both approaches and works from the inside out. This is an agent that is embedded directly into a running system and analyzes everything that happens: from code processing and requests to application behavior in real time
What is IAST used for?
IAST is needed to identify vulnerabilities as accurately as possible and minimize the number of false positives. Imagine you have a complex web application. The IAST scanner connects to it like a regular user, but at the same time monitors from the inside how the application works: what data passes through the methods, what happens with queries to the database, how parameters are processed, etc. That is, if DAST sees that “something went wrong,” then IAST can immediately highlight a specific section of code or library in which there is a problem
How does it work?
IAST is injected into an application while it is running, typically through a special agent that runs with the application. The agent analyzes code execution in real time: intercepts function calls, watches how data travels from the user to the database and back. As a result, we get a combination: the accuracy of static analysis + the practicality of dynamic
This is convenient at least because IAST doesn’t just say “you have XSS”, but shows “here, in such and such a line of code, when entering a parameter, the call went to such and such a function, and it was this function that opened the hole.” This is a huge plus for developers, because they don’t have to guess where exactly to dig
How to use IAST?
Usually IAST is installed on a test environment, but sometimes it is also installed on “production” servers - in order to catch problems directly in real traffic ( although there are nuances regarding performance and security ). Integration can be with CI/CD or during QA testing
Tools for Implementing IAST
There is almost no pure open source under IAST ( unlike SAST/DAST ). These are mainly commercial solutions. Among Western instruments - Contrast Security, Seeker. Russian players - PT Application Inspector ( IAST is built into the tool ) and Solar appScreener ( it also knows hybrid analysis modes )
I hope the picture now lines up better: SAST looks at the code, DAST looks at the application from the outside, and IAST combines and looks directly from the inside. Next time we’ll talk about another interesting class of solutions
#information_security #iast
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.