Posts
Lord, just when you want to go to bed, they give you material for the channel 🙄 Due to t…
February 7, 2025 at 1:41 AM•Max Knyazev is typing…Telegram mirror
Lord, just when you want to go to sleep, they give you material for the channel
🙄
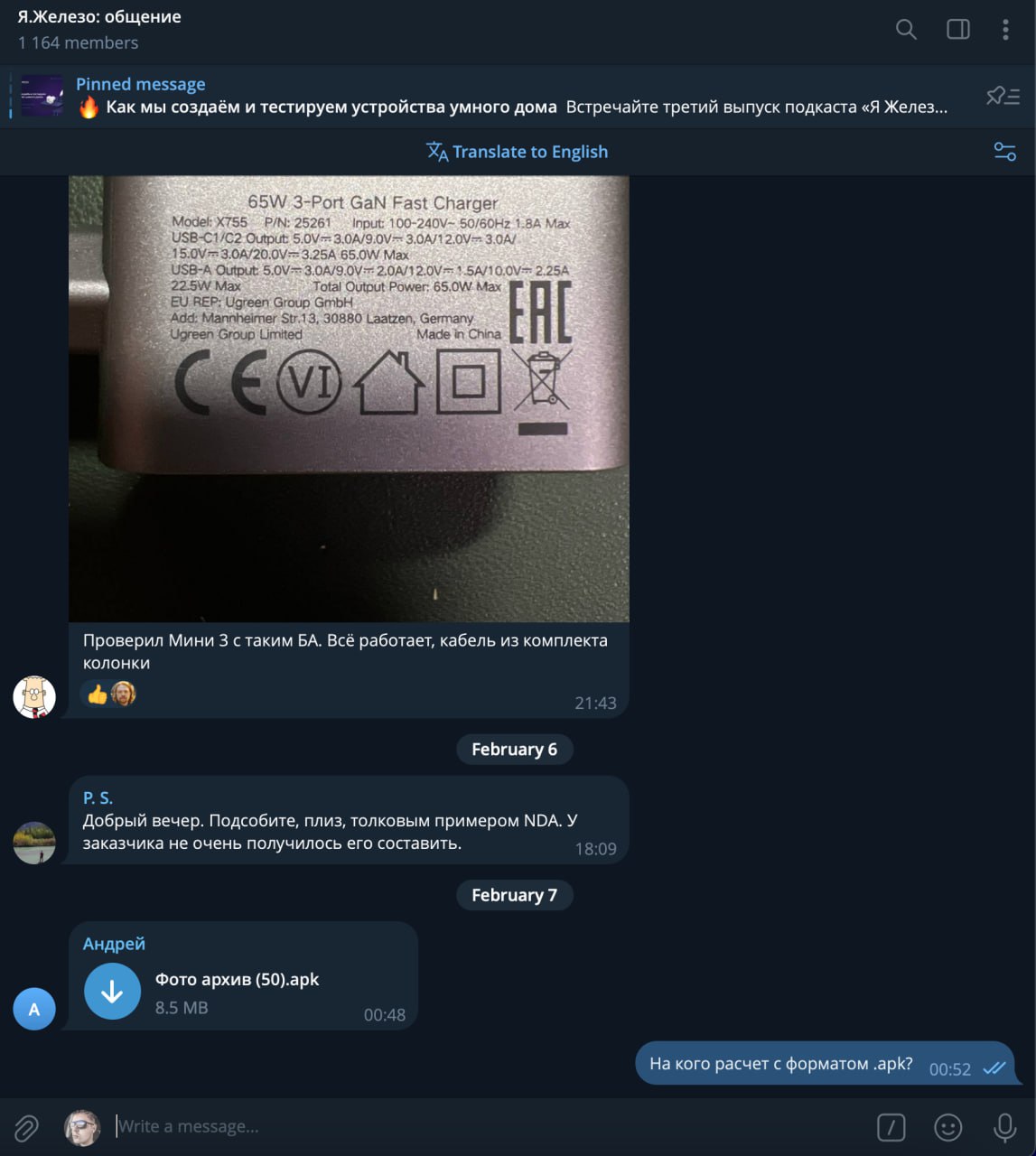
Due to the diversity of my interests, I am a member of various channels and chats. One of these chats is Ya.Zhelezo ( chat on Yandex hardware conferences, where they talk about hardware ). And literally just one of the “new arrivals” sent a file with a very interesting name - "Photo archive (50).apk"
😎
Oh, and in vain, because I’m not able to pass by this at all. Let's sort this out one by one. If any of my subscribers don’t know why you can’t download this, please read this post and the materials that I will attach to it . Protect yourself ( and maybe not only )
🥺
Let's start with what should generally confuse us in the first place - the file extension. As if the very name "Photo Archive" suggests that this must be something with .zip or .rar ( or something like that ). There's something strange here for some reason .apk . What exactly is this extension?
🧐
This, in turn, should lead us to believe that this thing wants to be installed on an Android device as an application ( or some kind of software ). And that's bad. Why? Now read as carefully and thoughtfully as possible
Just the other day, my friends published an article on Habré "Android Trojan Mamont - investigation of a real case of a new financial cyber threat" ( I even participated a little in its writing, but, really, very little ). There they analyze in as much detail as possible in practice this case with “photo archives” with the .apk extension. If you're interested, read the article itself, and in the meantime I'll describe what the guys ended up with
🏋♀
What is it?
It's simple, it's a new banking Trojan "Mamont" ( yes, yes, in the words of one famous pyromide builder throughout the CIS ). It is delivered through phishing schemes - either through fake online store sites with order trackers, or through messages from strangers ( like this message with the name of the archive “Are these your photos?” ) with a malicious file
👮♂
After installation at The application requests a wide range of permissions. It secretly installs services to intercept SMS, access the clipboard, monitor calls and even work with banking data ( view balance, transfer funds )
💣
Next, the guys discovered that the application establishes a connection with the C2 server ( IP 5.9.230.13) through non-standard ports and sends data in the form of POST requests. The Trojan code is modular - individual components are responsible for banking transactions, interception of messages, and more.
💸
To put it simply, by downloading and installing this file “Photo archive.apk”, you will allow attackers to access your personal and banking data, intercept messages and manipulate various information on the device ( here it depends on the imagination and abilities of specific attackers )
☠
Let's end this post with a little advice from me personally - guys, don't download anything from people you don't know . Always look at the extension. In general, be suspicious and cautious about everything that comes to you from unfamiliar numbers. If you pick up viruses and Trojans, and then change all your cards and documents - do you need it? Please take care of yourself and be careful
🆘
Good night everyone
😴
#information_security
Open original post on TelegramDue to the diversity of my interests, I am a member of various channels and chats. One of these chats is Ya.Zhelezo ( chat on Yandex hardware conferences, where they talk about hardware ). And literally just one of the “new arrivals” sent a file with a very interesting name - "Photo archive (50).apk"
Oh, and in vain, because I’m not able to pass by this at all. Let's sort this out one by one. If any of my subscribers don’t know why you can’t download this, please read this post and the materials that I will attach to it . Protect yourself ( and maybe not only )
Let's start with what should generally confuse us in the first place - the file extension. As if the very name "Photo Archive" suggests that this must be something with .zip or .rar ( or something like that ). There's something strange here for some reason .apk . What exactly is this extension?
.apk is the Android application file format used by the Android operating system
This, in turn, should lead us to believe that this thing wants to be installed on an Android device as an application ( or some kind of software ). And that's bad. Why? Now read as carefully and thoughtfully as possible
Just the other day, my friends published an article on Habré "Android Trojan Mamont - investigation of a real case of a new financial cyber threat" ( I even participated a little in its writing, but, really, very little ). There they analyze in as much detail as possible in practice this case with “photo archives” with the .apk extension. If you're interested, read the article itself, and in the meantime I'll describe what the guys ended up with
What is it?
It's simple, it's a new banking Trojan "Mamont" ( yes, yes, in the words of one famous pyromide builder throughout the CIS ). It is delivered through phishing schemes - either through fake online store sites with order trackers, or through messages from strangers ( like this message with the name of the archive “Are these your photos?” ) with a malicious file
After installation at The application requests a wide range of permissions. It secretly installs services to intercept SMS, access the clipboard, monitor calls and even work with banking data ( view balance, transfer funds )
Next, the guys discovered that the application establishes a connection with the C2 server ( IP 5.9.230.13) through non-standard ports and sends data in the form of POST requests. The Trojan code is modular - individual components are responsible for banking transactions, interception of messages, and more.
To put it simply, by downloading and installing this file “Photo archive.apk”, you will allow attackers to access your personal and banking data, intercept messages and manipulate various information on the device ( here it depends on the imagination and abilities of specific attackers )
Let's end this post with a little advice from me personally - guys, don't download anything from people you don't know . Always look at the extension. In general, be suspicious and cautious about everything that comes to you from unfamiliar numbers. If you pick up viruses and Trojans, and then change all your cards and documents - do you need it? Please take care of yourself and be careful
Good night everyone
#information_security
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.