Essay
Information Security Specialist Diploma. Part No. 1 - Methodology for ensuring the security of Internet of Things devices
How it all started Hello, Habr! My name is Max and this is my first article. At the same time, this article is also the last... my last article as a student in the field of "Computer Security"....
Where it all started
Hello, Habr!
My name is Max and this is my first article. At the same time, this article is also the last... my last article as a student in the “Computer Security” direction. It so happened that I will graduate from the university in February 2024 (the direction 10.05.01 “Computer Security” is a specialty, so students traditionally graduate in the winter after 5.5 years of study). Accordingly, already in the past 2023, before me, as well as before my colleagues in the specialty and course, the need arose to write a final qualifying work (in other words, a diploma) to obtain the qualification of an information security specialist and subsequent inevitable expulsion from the university.

Expulsion from the university with and without a diploma as an information security specialist according to the DALL-E neural network
Since I have a soft spot for “smart” (and sometimes not so smart) devices, the Internet of Things, and also love to create and create, I decided to develop ideas for my graduation project in this direction. The specifics of my specialty quite strictly set the focus on security, so the option “assemble the device, write the firmware and be happy with the work done” was not possible for me. It was necessary to come up with a research topic in such a way that I could satisfy both my creative needs and ideas IS .
After a brainstorming session with my supervisor, and also keeping in mind that the letter “B” in the phrase “Internet of Things” means “security” (if anyone hasn’t noticed, it’s not there), the topic of my future diploma at that time was formulated.
Thesis topic
It was decided to write a thesis on the topic “Methodology for ensuring the security of Internet of Things devices” . Upon initial perception of this proposal, it may seem that this is something from the category of “paper” information security with a clear emphasis on standards and legislation in the field of information security. In fact, this is not the case, which will become obvious upon further examination of the project.
Taking into account the fact that the very concept of the Internet of Things is problematic from a security point of view, the relevance of the study can be justified by the increased level of user security risks against the backdrop of the growing popularity of Internet of Things devices. In this regard, there is an undeniable need to improve the security of such devices. Through the development of device security practices IoT and it turned out to set the vector of the thesis, aimed primarily at safety. At the same time, it is necessary to understand that it is not enough to formulate and propose a methodology. It needs to be tested at least within a laboratory bench. And now, thanks to this concept, the creative power inherent in me is closed. the need to create devices.
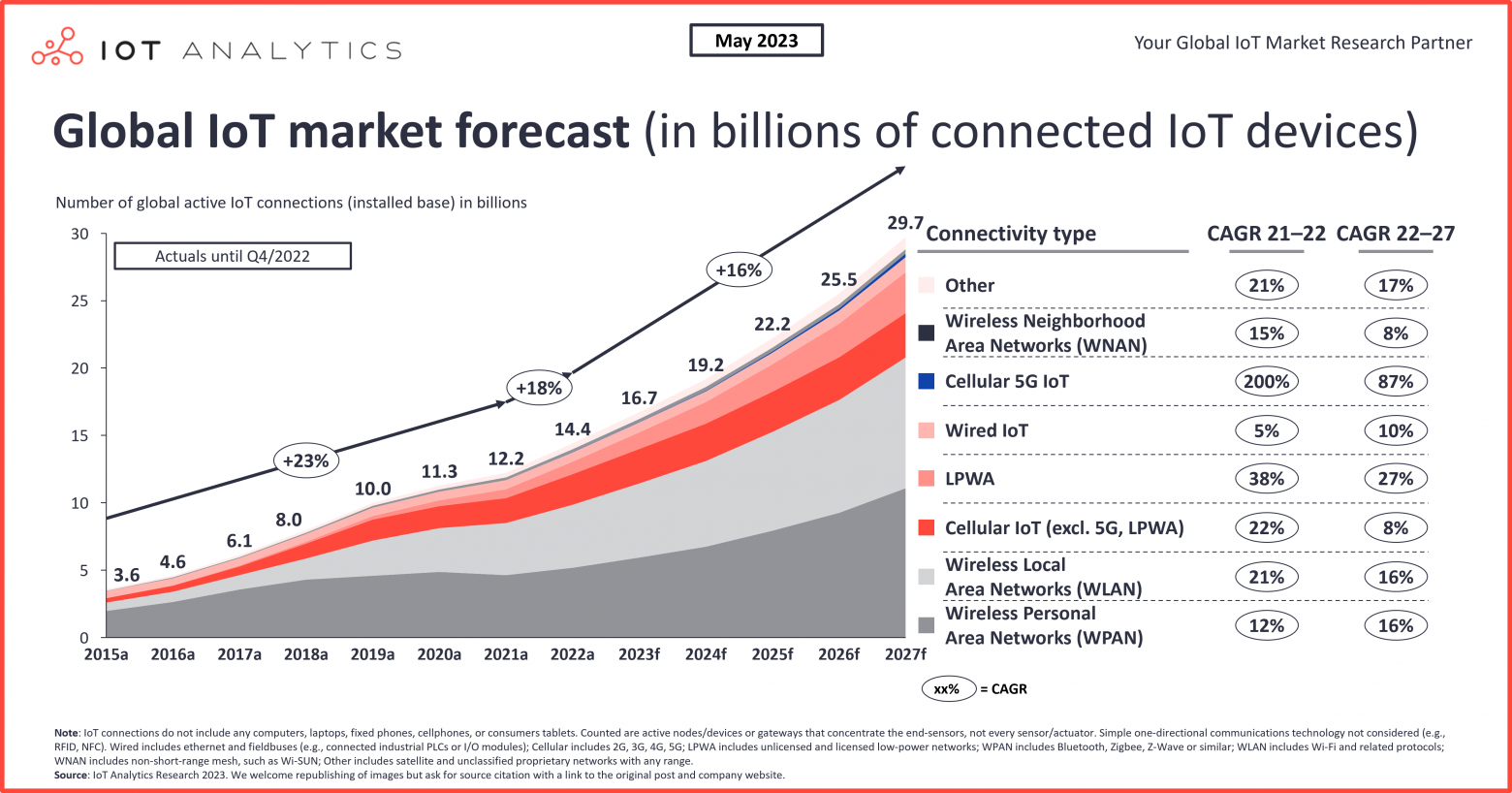
Statistics and forecasts for the growth of the number of Internet of Things devices around the world
Wireless data technology
Since the idea of the Internet of Things itself does not imply the use of a specific wireless data transmission technology, I was faced with the task of determining what exactly I would work with. The choice was made in favor of Bluetooth Low Energy, since I am mainly interested in portable devices, and this technology is one of the most popular in this segment.
Accordingly, the structure of the diploma began to emerge. It is clear that the result of the work should be a methodology for ensuring the security of Internet of Things devices using technology as a communication protocol BLE . Obviously, it needs to be formed on the basis of something, applied in the development of something, and then make sure of its effectiveness in some accessible way in a fairly short time for writing a thesis.
Objectives of the thesis
Based on this logic of reasoning, I identified the following logical tasks for the diploma:
-
Understand BLE technology . Consider the protocol stack, architectural features, vulnerabilities and vectors of the most common attacks on devices using this technology;
-
Define mechanisms to secure IoT devices using BLE . This is the basis on which the security methodology is formed;
-
Formation of a mathematical model based on multi-criteria selection . The idea was the following: the development of any devices (and not only) is carried out under conditions of restrictions. These may be financial or time constraints, skills and capabilities of the project team, etc. This kind of framework does not make it possible to implement all available protection mechanisms. In the end, there is the invisible hand of the market and other factors that affect the level of security of devices (as well as quality, price, and many other parameters of the final product). Although for many this may seem like something wild, companies and their managers are not always ready to allocate funds (not only financial) for IS . Remember how often you take care of your health during periods when you are not sick. The situation is similar. A mathematical model is needed to determine the highest and lowest priority protection mechanisms, so that development teams can take into account at least the most important of them and the end devices are much safer;
-
Formation of security methodology . The essence of the methodology actually follows from determining the priority of protection mechanisms using a mathematical model;
-
Development of a stationary device without protection . In order to have a “default” unprotected Internet of Things device;
-
Development of a wearable device with protection . Demons tradition of practical application of the technique;
-
Mobile application development . I wanted to interact with devices in the most comfortable way, and I had a desire to work a little with Flutter;
-
Attempts of unauthorized access to developed devices . By doing this, you can try to prove the effectiveness of the resulting technique.
Final qualifying work
Structurally, the diploma was divided into research (technology BLE ), design (protection mechanisms, mathematical model and methodology) and technological (devices, application, NSD ) parts.
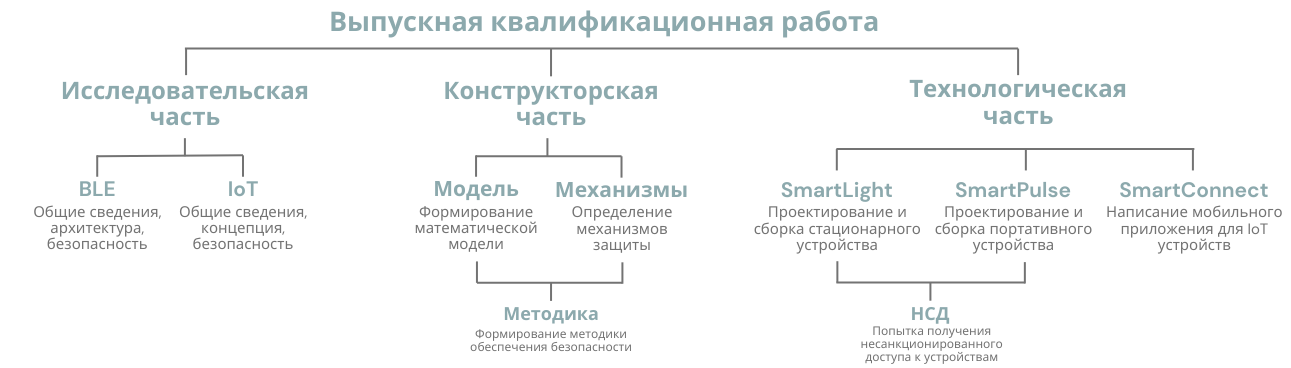
Structure of final qualifying work
Everything is clear with the research part - familiarizing yourself with various sources, surfing the Internet and analyzing everything you read. Much has been said about BLE and repeatedly by much more authoritative and experienced people in this matter. Here I can recommend the book “Intro to Bluetooth Low Energy: The easiest way to learn BLE”, translation which, by the way, is on Habré.
Mathematical model
With the technological part, everything is much more interesting. To develop a mathematical model, on the basis of which the priority of each protection mechanism will be calculated in the future, it is necessary to determine the indicators of this priority. In essence, these are criteria that tend to a certain minimum or maximum, based on the results of which it is possible to draw conclusions about how important a particular protection mechanism is relative to other mechanisms. As described earlier, I considered the option of multicriteria selection, and this is what I ultimately decided to choose when creating a mathematical model.
This is how DALL-E imagines the formation of a mathematical model :)
Priority indicators
The following priority indicators were determined:
-
providing protection against the greatest number of different types of attacks
-
complexity of the mechanism implementation
I acted from the logic that the protection mechanism should ensure the safety of the device from many different types of attacks. For example, a conditional dynamically changing PIN code for connecting to a device, in theory, can help protect against both unauthorized access to the device and man-in-the-middle attacks.
I would not like to pretend to be the ultimate truth, but I tried to look for all sorts of scenarios for using various protection mechanisms in the context of countering the main types of attacks. Therefore, in my understanding, a well-implemented mechanism can help prevent not just one specific attack, but a whole range of similar attacks.
The complexity of implementing the mechanism should be taken into account precisely based on the factors of limited resources that I mentioned earlier. If all resources, including financial and time, tended to infinity, this indicator would not be relevant, but, unfortunately or fortunately, this does not happen. Based on this, it is important to understand that “complexity” will be a highly subjective concept, since what is difficult for one development team is quite simple for another. Poe Therefore, this indicator directly depends on the capabilities and resources of organizations, startups and individual development teams.
Sets
In the mathematical model I defined the following sets:
-
– many security mechanisms aimed at ensuring the security of an Internet of Things device using BLE technology,
is the set of indices of these measures.
-
– many security threats that are implemented in the form of attacks on the protected IoT device,
– a set of indices of these attacks (threats).
-
– many protection options (developer resources),
– a set of indexes of these possibilities.
-
– many factors that represent the need to implement certain protection mechanisms, where
– a set of indices of these factors.
In this case, the parameters of the set elements will be determined by the following relations:
-
– assessment of damage to the user of the IoT device in case of successful implementation
th threat.
-
– probability (or possibility) of occurrence
th attack (implementation of a threat) on an IoT device.
-
– probability (or possibility from the point of view of fuzzy sets) of prevention
-th attack (implementation of threat) when using
-th mechanism.
-
– complexity of implementation
-th mechanism.
-
– assessment of opportunities for implementation
-th mechanism.
-
– maximum “volume”
-th resources (financial, technical, personnel, professional, time, intellectual, etc.) that the developer is ready to allocate to ensure the security of the IoT device.
-
– a Boolean matrix that specifies the factors of the need to implement a certain mechanism,
, if
The th mechanism ensures the execution
th factor of the need for implementation,
- otherwise.
In the following I also denote the Boolean variable
,
if
-th mechanism is used for protection,
- otherwise. Variables form a vector
.
Priority indicators must use two necessary conditions:
-
Assessing damage prevented - providing protection against the greatest number of types of attacks on the device (must be maximized):
-
The complexity of implementing the protection mechanisms used (needs to be minimized):
Next you need to enter restrictions:
-
Restrictions on the use of resources when developing an IoT device:
-
Restriction on the factors of necessity for the implementation of the mechanism (the condition that any such factor must be fulfilled by the implementation of the mechanism):
Scorecard
The presented formulation of the problem with priority indicators is a multicriteria Boolean programming problem with two quality indicators. One indicator is nonlinear, the other is linear, linear constraints.
To summarize the mathematical research carried out, we highlight a system of indicators for optimization:
As a result, it was possible to reduce the mathematical formulation of the problem to the complexity of implementing a protection mechanism, which affects the ability to ensure the safety of device development, in conjunction with extracting maximum efficiency in preventing damage to the user of the device.
At the same time, it is necessary to take into account the limitations of the developer's capabilities and the limitations imposed by the factors necessary to implement protection mechanisms against certain types of attacks.
In order to combine these various indicators, it is necessary to normalize them, combining the ability of protection with the complexity of implementation. Considering that the first vector is aimed at achieving the maximum value, and the second tends to the minimum, I coordinated them for general analysis.
One approach to solving this problem is to transform the minimization problem into a maximization problem by adding a negative sign to the coefficients. Thus, the system of indicators for optimization, which I previously presented here, was transformed as follows:
where
– complexity of implementation
-th security mechanism, taken with the opposite sign, which allows you to turn the minimization problem into a maximization problem.
The formed system becomes a solution to the process of establishing a hierarchy of protective mechanisms through their prioritization, which is achieved by determining the most suitable protection mechanism at each iteration.
Essentially, this is all we need to begin drawing up a hierarchy of protection mechanisms (except for the protection mechanisms themselves) based on the priority of each of them. In the thesis itself, I consider in more detail the interactive method for solving a multicriteria problem, but in this article I see no point in touching on it, since it will not affect the solution of the already described model.
Protection Mechanisms
At this point, it makes sense to finish the math and consider the protection mechanisms. After analyzing information from the Internet on specialized resources and consulting with several colleagues from my work (I work as an information security engineer in one of the large domestic information security companies), I settled on the following protection mechanisms:
Protection Mechanisms
|
Protection mechanism |
Description of the mechanism |
|---|---|
|
Restricting access to critical memory areas |
Maintain system security by preventing improper or malicious access to sensitive memory areas, helping to avoid threats such as buffer overflows |
|
Data and firmware encryption |
Protects device information and software by converting data into an encrypted format that is only accessible with the appropriate decryption key |
|
Random number sequence generators |
Strengthening system security by generating random number sequences that are used to generate cryptographic keys and passwords for authentication |
|
Download only official oh firmware |
Increasing device reliability by allowing installation of only verified updates and firmware, preventing risks from malware or unauthorized changes |
|
Dynamic pin code authentication |
Strengthen protection against unauthorized access by using temporary or changing PIN codes, making them more resistant to hacking |
|
Non-Bypass Authentication Mechanisms |
Increasing the level of system security by establishing strict authentication procedures that exclude the possibility of bypassing or hacking them |
|
Secure connection |
Ensuring the security of data transferred between devices using encryption methods and connection security |
|
Distribution of encryption keys during pairing |
Improve the security of communications between devices by securely transferring the cryptographic keys needed to encrypt data |
|
Encryption key storage options |
Strengthen the security of stored encryption keys by configuring their secure storage and use |
|
Using the latest BLE and Bluetooth specifications |
Improve device security and performance by leveraging the latest and most updated Bluetooth standards |
|
Restricting access to BLE services |
Improve system security by controlling and limiting access to Bluetooth features and services, preventing unauthorized use |
|
Updating firmware and encryption keys |
Keep your device secure by keeping both software and security keys up to date |
|
Protecting the firmware update process |
Guarantees security when updating software by preventing the possibility of malware being introduced during the update process |
|
Intrusion detection and prevention systems |
Actively protects devices from unauthorized access attempts or attacks using algorithms to monitor and respond to suspicious activity |
|
Machine learning algorithms for anomaly detection |
Improving the system's ability to detect and respond to unusual actions or threats that potentially indicate a security compromise |
|
Anonymization of confidential data |
Protect sensitive information by de-identifying or deleting it before transmission or storage, preventing data leakage |
|
Chips with security mechanisms (Secure Element) |
Implementation of special integrated circuits designed to protect data at the hardware level. Ensuring the secure storage of sensitive data such as cryptographic keys |
|
Specialized housings and seals |
The use of physical barriers designed to protect the internal components of a device from unauthorized access. Preventing tampering or modification of the device |
|
Isolation of the BLE module from the main logic |
A method for isolating a BLE module from the main system of the device. Preventing the possibility of spread threats from the BLE module to other important parts of the device. |
|
External Safety Modules (HSMs) |
The use of physical devices designed to manage digital keys and perform cryptographic operations in a secure environment isolated from the device's main system. |
|
Device tamper detection mechanisms |
The use of sensors or systems that respond to unauthorized attempts to access the internal components of the device |
|
Protection against electromagnetic attacks |
Measures designed to protect the device from attacks based on electromagnetic fields that can affect electronic components and data |
|
Biometric authentication technologies |
Authentication methods that use a person's unique physiological or behavioral characteristics, such as fingerprints, facial recognition, or voice recognition |
|
Security measures at all stages of development |
Integrating security practices into every step of the development process, from architecture to coding to testing, to ensure overall system security |
|
Automatically reset or turn off the device |
Use automated procedures to protect your device in emergency situations, such as system hangs or detection of unauthorized access attempts, helping prevent potential security threats |
|
Limiting physical interaction |
Restrict access to device features, such as not displaying or recording information, to minimize the risk of data leakage or unauthorized use |
|
Signal Jamming Warning |
Use of a mechanism that actively monitors and alerts on attempts to jam or interfere with wireless signals. Detection and prevention of attacks aimed at disrupting the correct operation of a device’s wireless communications |
|
Using location to activate protection |
Use a device's geographic location to make decisions about enabling or disabling certain security features |
|
Limit on number of connections |
Limiting the number of devices that can connect to an IoT device |
I in no way claim the completeness of the mechanisms provided, nor the correctness of some of my arguments and judgments. I did not try to cover all the ways and means of implementing protection mechanisms in devices, since I could write a separate article (if not a book) on this topic. Judgments are based on my knowledge and experience, so I cannot claim that this is the most correct option. Of course, this list of mechanisms can and should be expanded, modified and developed.
After identifying and classifying protection mechanisms, they can be prioritized to prevent various types of attacks and complexity of implementation using a previously developed mathematical model.
Determining the weight of priority indicators
When determining the “weight” of indicators of protection mechanisms, we will proceed from the fact the fact that there are no more dangerous attacks or less dangerous ones. In this case, any attack or threat will be equated to gaining access to information in an illegitimate manner. Accordingly, the “weight” of the indicator for the number of prevented attacks for each protection mechanism will be calculated relative to other mechanisms in such a way that the total when calculating this criterion for all mechanisms is one. I determined the “weight” of the implementation complexity indicator in a similar way.
To begin with, we define for each security mechanism the threats and attacks that can be prevented through its implementation during the development of an Internet of Things device. We will also calculate their number for each mechanism and provide the rationale for our decision.
Countermeasures against various types of attacks
|
Protection mechanism |
Attack type |
Rationale |
|---|---|---|
|
Restricting access to critical memory areas |
Buffer overflow attacks |
Restricting access to critical memory areas prevents this type of attack by blocking the ability to write data beyond the allocated buffer. |
|
Code Execution Attacks |
By restricting access to certain areas of memory, you can prevent malicious code from executing, even if it was introduced via a buffer overflow attack | |
|
Side channel attacks |
Memory access restrictions can reduce the risk of information leakage through side channels because sensitive data and operations are protected and isolated | |
|
Manipulating data and device state |
By limiting access to memory, you can prevent unauthorized changes to critical data and configurations that could be changed during an attack to control the device or its functions | |
|
Data and firmware encryption |
Interception and unauthorized access to data |
Encryption prevents third parties from reading and understanding the intercepted data |
|
Man-in-the-middle attacks |
Even if the data was intercepted, it cannot be read or modified without detection | |
|
Injecting malware through firmware |
Encrypting the device firmware prevents it from being modified or replaced with malicious versions without the appropriate decryption key, which protects the device from the introduction of malicious software | |
|
Leakage of confidential information |
Encrypting data stored on the device protects sensitive information, such as users' personal data or business information, from being accessed if the device is physically captured | |
|
Data integrity attacks |
Encryption can also ensure data integrity when used in conjunction with mechanisms such as digital signatures, preventing unauthorized modification of data | |
|
Random number sequence generators |
Brute force attacks |
Random numbers used to create complex passwords or keys significantly increase the complexity and time required to guess them during brute-force attacks |
|
Attacks on authentication mechanisms |
Many authentication systems, including one-time passwords (OTP) and two-factor authentication systems, rely on random number generation to create unique authentication codes that are difficult to predict or replicate | |
|
Attacks on session keys |
Reliable random number generators help ensure each session is unique | |
|
Attacks on cryptographic systems |
Robust random number generators provide the high level of "randomness" needed to securely strengthen cryptographic algorithms | |
|
Download only official firmware |
Injection of malware |
By prohibiting the installation of unofficial firmware, you can prevent attackers from introducing malware that could be used to steal data, spy on or remotely control the device. |
|
Dynamic pin code authentication |
Password guessing attacks |
Dynamic PIN codes, which change frequently, make brute-force attacks much more difficult because attackers need to guess the PIN code in a limited amount of time before it changes |
|
Reuse attacks |
Since a dynamic PIN is only valid for a short time, it prevents it from being reused by attackers if it was somehow intercepted | |
|
Phishing attacks |
Dynamic PINs reduce the risks associated with phishing attacks because even if a user unwittingly reveals their PIN, it will quickly become invalid | |
|
Unauthorized access |
Using a dynamic PIN code for authentication makes unauthorized access attempts much more difficult, since a potential attacker needs to know the current valid PIN code | |
|
Social engineering |
Because dynamic PINs change regularly, they are less susceptible to risks associated with social engineering or guessing passwords based on the user's personal information | |
|
Non-Bypass Authentication Mechanisms |
Unauthorized access |
Bypass-resistant authentication systems reduce the likelihood that an attacker can gain access to a device or network by exploiting weaknesses in authentication procedures. |
|
Phishing attacks |
The difficulty of bypassing the authentication system makes phishing attempts useless | |
|
Social engineering |
Similar to phishing | |
|
Brute force attacks |
Non-bypass authentication systems often include mechanisms to prevent or make brute force attacks much more difficult, for example by temporarily blocking access after multiple failed login attempts. | |
|
Secure connection |
Man-in-the-middle attacks |
Secure connections prevent data sent between devices from being intercepted and modified, a key component of MitM attacks |
|
Data interception |
Encrypting data within a secure connection makes the intercepted data useless to an attacker s, since they cannot decrypt the information without the corresponding key | |
|
Unauthorized access |
Secure connections often include authentication mechanisms, thereby preventing access by unauthorized devices | |
|
Data injection and session falsification |
Secure connections prevent the introduction of malicious data into a communication session, as well as attempts by attackers to impersonate a trusted device | |
|
Data integrity attacks |
Encryption and authentication of data in a secure connection ensures that the data has not been modified during transmission, ensuring its integrity | |
|
Distribution of encryption keys during pairing |
Man-in-the-middle attacks |
By distributing encryption keys during the pairing process, a secure connection is created that eliminates the possibility of interception and modification of data by third parties |
|
Intercepting encryption keys |
Secure key distribution mechanisms ensure that encryption keys are transmitted confidentially and without risk of interception, which is critical to maintaining the integrity of a secure connection | |
|
Unauthorized access |
Secure key distribution during the pairing process ensures that only authorized devices can establish encrypted connections, thereby preventing unauthorized devices from accessing the network and transmitting data | |
|
Leakage of confidential information |
Secure key distribution ensures that sensitive data transferred between devices is encrypted and cannot be read if intercepted | |
|
Data integrity attacks |
Because encryption keys are used to ensure the integrity of transmitted data, their secure distribution helps prevent attacks aimed at altering or tampering with data. | |
|
Encryption key storage options |
Unauthorized access |
Setting strict key storage parameters helps prevent key theft or unauthorized access |
|
Restoring keys after a device has been compromised |
Effective key management includes mechanisms for securely destroying or replacing keys if a device is lost or compromised | |
|
Using the latest BLE and Bluetooth specifications |
Vulnerabilities in older versions of Bluetooth |
Older versions of Bluetooth may contain vulnerabilities that have been fixed in newer specifications |
|
Man-in-the-middle attacks |
The latest standards include advanced encryption and authentication methods that make it more difficult to carry out MitM attacks | |
|
Unauthorized access |
Modern BLE specifications include improved authentication and key negotiation methods, which increases the difficulty of unauthorized access | |
|
Attacks on Confidentiality and Integrity |
Updated specifications provide better data protection by preventing data from being intercepted and altered in transit. | |
|
Attacks on cryptographic systems |
Newer versions of Bluetooth offer stronger and more secure encryption algorithms iya, increasing the level of protection of transmitted data | |
|
Restricting access to BLE services |
Unauthorized access |
By restricting access to BLE services, you can prevent unauthorized use or management of the device, preventing outsiders from controlling the device without proper permissions. |
|
Data privacy attacks |
Access restriction helps protect sensitive data transmitted or stored on your device from interception and unauthorized viewing | |
|
Man-in-the-middle attacks |
Restricting access to BLE services can also make MitM attacks more difficult by making it more difficult for an attacker to intercept or tamper with data in transit. | |
|
Updating firmware and encryption keys |
Vulnerabilities in old firmware |
Regular firmware updates help fix known vulnerabilities and bugs, which prevents attackers from exploiting these weaknesses |
|
Unauthorized access |
Updated encryption keys and algorithms improve protection against attacks designed to intercept or modify data | |
|
Attacks on old versions of BLE |
Regular updates may include improvements to the BLE protocol, eliminating vulnerabilities and improving overall wireless security | |
|
Protecting the firmware update process |
Attacks on the update process |
Protecting the update process prevents the risk of malware being introduced into the device during the update, which could lead to compromise of the device or the entire network |
|
Man-in-the-middle attacks |
Protecting the transfer of firmware updates from interception and spoofing is important to prevent MitM attacks, in which an attacker can try to replace the update with a malicious one. | |
|
Unauthorized changes to the firmware |
Update protection ensures that only authorized changes are applied to the device, preventing changes that could introduce new vulnerabilities or break device functionality | |
|
Intrusion detection and prevention systems |
Unauthorized access |
IDPS can detect and block unauthorized attempts to access devices or networks, preventing potential hacks and data leaks |
|
Man-in-the-middle attacks |
Systems can detect traffic anomalies that indicate MitM attacks | |
|
Injection of malware |
IDPS can detect attempts to inject malware into IoT devices and take action to block or remove it | |
|
Data leak |
Detecting unusual data transmission patterns can help identify and prevent data leaks | |
|
Machine learning algorithms for anomaly detection |
Early detection of malware |
Algorithms can identify anomalous behavior caused by malware, making it possible to intervene more quickly to ensure device security |
|
Ada response to new threats |
One of the key benefits of machine learning is the ability to adapt to new threats as they emerge through continuous learning based on current data. | |
|
Detecting unusual behavior |
Machine learning algorithms can analyze patterns of normal device behavior and detect deviations from that pattern, which could indicate intrusion, attack, or malfunction | |
|
Anonymization of confidential data |
Breach of confidentiality |
By removing or changing personal identifiers in data, anonymization helps ensure the privacy of user information |
|
Data leak |
Data anonymization ensures that even if information is leaked, it cannot be used to identify specific individuals, which significantly reduces the risk of abuse | |
|
Chips with security mechanisms (Secure Element) |
Physical attacks and unauthorized access |
Secure Element provides secure hardware storage that is resistant to physical attacks and unauthorized access attempts, helping to protect critical data and encryption keys |
|
Data and key leaks |
Storing sensitive data and encryption keys in Secure Element protects it from software attacks and leaks, which is especially important for operations that require a high level of security | |
|
Data manipulation |
Secure Element integration ensures data integrity and authenticity, preventing unauthorized changes | |
|
Specialized housings and seals |
Physical attacks and unauthorized access |
Specialized housings and seals protect devices from physical tampering, such as unauthorized access to internal components or modification of the device |
|
Tampering (device manipulation) |
The use of seals and protective enclosures can help detect tampering attempts, warning of possible compromise of the device | |
|
Security risks associated with physical attacks |
Attempts to connect external devices or illegally read data can be prevented by physical barriers | |
|
Injection of malicious devices or components |
Secure enclosures can prevent malicious devices or components from being introduced into the device enclosure | |
|
Environmental protection |
Specialized cases can protect devices from external factors such as water, dust, etc., which increases their reliability and durability | |
|
Isolation of the BLE module from the main logic |
Protecting essential device functions |
In the event of vulnerabilities or attacks on the BLE module, the main system of the device remains protected, which ensures that important functions continue to function |
|
Preventing unauthorized access |
BLE module isolation makes it difficult for attackers to access the device's core system via BLE, which improves overall device security | |
|
External Safety Modules (HSMs) |
Physical attacks and unauthorized access |
HSMs provide physical security for encryption keys and other sensitive data, protecting them from physical hacking attempts and unauthorized access |
|
Leaked encryption keys |
HSMs prevent encryption keys from leaking by ensuring they are securely stored and processed in a secure environment | |
|
Resistance to hardware attacks |
HSMs are designed to resist hardware attacks such as side channel attacks or electromagnetic radiation attacks | |
|
Device tamper detection mechanisms |
Physical attacks and tampering |
Tamper detection mechanisms help identify attempts to physically access a device, such as tampering with the chassis to access internal components, tampering, or introducing malicious devices |
|
Tamper protection |
When a device is detected to be tampered with, you can automatically take security measures such as locking the device, notifying administrators, or even deleting sensitive data | |
|
Protection against electromagnetic attacks |
Electromagnetic Interference (EMI) |
EMI protection helps prevent accidental or deliberate attempts to tamper with the device by creating external electromagnetic fields |
|
Damage to electronics |
Strong electromagnetic fields can physically damage electronic components. Protection against these fields improves the reliability and longevity of devices | |
|
Biometric authentication technologies |
Password guessing attacks |
Biometric authentication prevents such attacks because biometric data is much more difficult to guess or reproduce compared to standard passwords |
|
Phishing and Social Engineering Threats |
Biometric authentication reduces the risks associated with credential theft because biometric data cannot be easily shared or stolen through phishing or social engineering | |
|
Unauthorized physical access |
The use of biometric technologies in access control systems improves protection against unauthorized physical access to protected devices | |
|
Security risks when you lose your device |
If your device is lost or stolen, biometric authentication helps prevent unauthorized access to data | |
|
Identity spoofing attacks |
Biometric data is unique to each individual, making it difficult to spoof identity to gain access to devices or systems | |
|
Security measures at all stages of development |
Software vulnerabilities |
Implementing security measures early and taking them into account during the design phase helps prevent the creation of code with vulnerabilities that can be exploited by attackers |
|
Attacks on components and interfaces |
Attention to security when designing hardware components and interfaces reduces the risk of physical attacks and attacks to device interfaces | |
|
Compatibility and security issues in updates |
Planning and testing firmware and software updates with security in mind prevents new vulnerabilities and outages | |
|
End user threats |
Incorporating security considerations into user interface design and documentation helps reduce the risk of device misuse and related threats. | |
|
Exploiting vulnerabilities in third-party components |
Careful analysis and selection of third-party libraries and components increases the security and resistance of the device to external threats | |
|
Automatically reset or turn off the device |
Detection and prevention of unauthorized access |
If the system detects an unauthorized access attempt or other suspicious activity, automatic shutdown can prevent further hacking attempts |
|
Protection against software failures |
Automatic reset can help when software gets stuck or crashes, allowing the device to restore normal operation without user intervention | |
|
Limiting physical interaction |
Physical attacks and tampering |
By limiting physical access to the device, you can prevent unauthorized attempts to open, modify, or tamper with the device. |
|
Injection of malicious devices |
Restricting access to physical device ports, such as USB or connection ports, helps prevent malicious devices or storage media from being connected | |
|
Device theft |
Restricting physical access helps protect devices from theft, which is especially important for devices located in publicly accessible or low-visibility areas | |
|
Signal Jamming Warning |
Signal jamming attacks |
Detection of signal jamming attempts helps prevent attacks that aim to disrupt wireless communications between IoT devices, which could cause them to go offline or fail to function. |
|
Preventing unauthorized access |
In some cases, jamming attacks may be a precursor to a hacking or physical intrusion attempt. | |
|
Using location to activate protection |
Prevent theft or unauthorized use |
If the device is moved outside the predefined area, additional security measures may be activated to prevent unauthorized use or theft. |
|
Limit on number of connections |
Denial of service attacks |
By limiting the number of connections, you can prevent the device from being overwhelmed by a large number of requests, which is a typical DoS attack tactic. |
|
Unauthorized access and man-in-the-middle attacks |
By limiting the number of simultaneous connections, the likelihood of unauthorized access is reduced. rogue or suspicious connections | |
|
Distributed denial of service attacks |
Just as with DoS attacks, limiting connections helps protect devices from being overloaded in the event of massive attacks from multiple sources. |
Having identified the main attacks and threats that can be prevented by each individual mechanism, I compiled a table defining the complexity of implementing all mechanisms. When determining complexity, I decided to use a 10-point system and the subjectivity of the possibilities for implementation. I assessed the complexity solely in relation to the complexity of implementing other mechanisms.
For maximum complexity, I took the most comprehensive protection mechanism - the introduction of security principles at all stages of device development, since this mechanism requires the greatest amount of knowledge and practical skills in the field of secure development, vulnerability analysis, practical security principles and spends a fairly large amount of financial and time resources.
Assessing the complexity of implementing protection mechanisms
|
Protection mechanism |
Implementation complexity assessment |
Rationale |
|---|---|---|
|
Restricting access to critical memory areas |
5 |
Often implemented in software |
|
Data and firmware encryption |
7 |
Requires the development and integration of strong encryption algorithms, which can be complex and costly |
|
Random number sequence generators |
5 |
Implementing quality random number generators requires specialized knowledge and can be challenging |
|
Download only official firmware |
6 |
It is necessary to provide reliable mechanisms for verifying the authenticity and integrity of the firmware |
|
Dynamic pin code authentication |
4 |
Requires development and implementation of logic for generating and managing dynamic codes |
|
Non-Bypass Authentication Mechanisms |
7 |
Difficulty in implementing strong, non-bypassable authentication mechanisms |
|
Secure connection |
7 |
Requires the development and implementation of reliable secure connection protocols |
|
Distribution of encryption keys during pairing |
6 |
The challenge lies in the secure and efficient distribution and management of keys |
|
Encryption key storage options |
6 |
Requires the development of reliable mechanisms for securely storing and managing keys |
|
Using the latest BLE and Bluetooth specifications |
4 |
Continuous monitoring and implementation of the latest technology standards is required |
|
Restricting access to BLE services |
6 |
Requires the development and implementation of access control mechanisms, which can be difficult depending on depending on the complexity of BLE services |
|
Updating firmware and encryption keys |
7 |
Difficulty in ensuring a reliable and secure update process, including development and testing |
|
Protecting the firmware update process |
7 |
Requires sophisticated security design to protect the update process from attacks |
|
Intrusion detection and prevention systems |
8 |
High complexity in the development and integration of complex intrusion detection and prevention systems |
|
Machine learning algorithms for anomaly detection |
8 |
The development and integration of machine learning algorithms requires significant resources and specialized knowledge |
|
Anonymization of confidential data |
5 |
Implementing effective data anonymization mechanisms requires careful planning and design |
|
Chips with security mechanisms (Secure Element) |
8 |
Requires specialized hardware integration and hardware-level optimization |
|
Specialized housings and seals |
6 |
Requires the development and production of specialized enclosures, which can be costly |
|
Isolation of the BLE module from the main logic |
7 |
Requires complex software development and hardware integration |
|
External Safety Modules (HSMs) |
9 |
High complexity of integration and high cost of external HSMs |
|
Device tamper detection mechanisms |
5 |
Easy to implement, but requires additional equipment |
|
Protection against electromagnetic attacks |
7 |
Difficult to implement, requires specialized materials and design |
|
Biometric authentication technologies |
8 |
Requires integration of complex biometric sensors and software |
|
Security measures at all stages of development |
10 |
Requires an integrated approach at all stages, including design, development and testing |
|
Automatically reset or turn off the device |
4 |
Relatively easy to implement, but requires setting trigger conditions |
|
Limiting physical interaction |
3 |
A simple measure, mainly depends on the design of the case |
|
Signal Jamming Warning |
6 |
Requires integration of monitoring and signal analysis systems |
|
Using location to activate protection |
5 |
Medium complexity, requires a location system and interaction logic |
|
Limit on number of connections |
2 |
Simple implementation via software connection restriction |
Next, we will simply combine both tables with the “weights” of indicators for each mechanism into one for the convenience of further interaction with them.
Weight of indicators for each mechanism
|
Mechanics ZM protection |
Implementation complexity |
Number of attack types |
|---|---|---|
|
Restricting access to critical memory areas |
5 |
4 |
|
Data and firmware encryption |
7 |
5 |
|
Random number sequence generators |
5 |
4 |
|
Download only official firmware |
6 |
1 |
|
Dynamic pin code authentication |
4 |
5 |
|
Non-Bypass Authentication Mechanisms |
7 |
4 |
|
Secure connection |
7 |
5 |
|
Distribution of encryption keys during pairing |
6 |
5 |
|
Encryption key storage options |
6 |
2 |
|
Using the latest BLE and Bluetooth specifications |
4 |
5 |
|
Restricting access to BLE services |
6 |
3 |
|
Updating firmware and encryption keys |
7 |
3 |
|
Protecting the firmware update process |
7 |
3 |
|
Intrusion detection and prevention systems |
8 |
4 |
|
Machine learning algorithms for anomaly detection |
8 |
3 |
|
Anonymization of confidential data |
5 |
2 |
|
Chips with security mechanisms (Secure Element) |
8 |
3 |
|
Specialized housings and seals |
6 |
5 |
|
Isolation of the BLE module from the main logic |
7 |
2 |
|
External Safety Modules (HSMs) |
9 |
3 |
|
Device tamper detection mechanisms |
5 |
2 |
|
Protection against electromagnetic attacks |
7 |
2 |
|
Biometric authentication technologies |
8 |
5 |
|
Security measures at all stages of development |
10 |
5 |
|
Automatically reset or turn off the device |
4 |
2 |
|
Limiting physical interaction |
3 |
3 |
|
Signal Jamming Warning |
6 |
2 |
|
Using location to activate protection |
5 |
1 |
|
Limit on number of connections |
2 |
3 |
Once it has been possible to determine and justify the “weights” of all indicators, you can begin to calculate the priority of each protection mechanism.
As mentioned earlier, in order to use one general formula characterizing the protection mechanism, the relative value of the implementation complexity indicator was taken into account with the opposite sign, thus formally minimizing complexity is reduced to searching for the maximum. For these purposes, the value in the table is It will also be written with a minus. In calculations, I rounded all values to hundredths.
Compliance of protection mechanisms with criteria
|
Goal |
Criteria | |
|---|---|---|
|
Preventing different types of attacks |
Implementation complexity | |
|
Criteria weight |
0.5 |
0.5 |
|
Protection Mechanisms |
Ability Assessment |
Difficulty rating |
|
Restricting access to critical memory areas |
0.038 |
-0.028 |
|
Data and firmware encryption |
0.047 |
-0.039 |
|
Random number sequence generators |
0.038 |
-0.028 |
|
Download only official firmware |
0.009 |
-0.034 |
|
Dynamic pin code authentication |
0.047 |
-0.022 |
|
Non-Bypass Authentication Mechanisms |
0.038 |
-0.039 |
|
Secure connection |
0.047 |
-0.039 |
|
Distribution of encryption keys during pairing |
0.047 |
-0.034 |
|
Encryption key storage options |
0.019 |
-0.034 |
|
Using the latest BLE and Bluetooth specifications |
0.047 |
-0.022 |
|
Restricting access to BLE services |
0.028 |
-0.034 |
|
Updating firmware and encryption keys |
0.028 |
-0.039 |
|
Protecting the firmware update process |
0.028 |
-0.039 |
|
Intrusion detection and prevention systems |
0.038 |
-0.045 |
|
Machine learning algorithms for anomaly detection |
0.028 |
-0.045 |
|
Anonymization of confidential data |
0.019 |
-0.028 |
|
Chips with security mechanisms (Secure Element) |
0.028 |
-0.045 |
|
Specialized housings and seals |
0.047 |
-0.034 |
|
Isolation of the BLE module from the main logic |
0.019 |
-0.039 |
|
External Safety Modules (HSMs) |
0.028 |
-0.050 |
|
Device tamper detection mechanisms |
0.019 |
-0.028 |
|
Protection against electromagnetic attacks |
0.019 |
-0.039 |
|
Biometric authentication technologies |
0.047 |
-0.045 |
|
Security measures at all stages of development |
0.047 |
-0.056 |
|
Automatically reset or turn off the device |
0.019 |
-0.022 |
|
Limiting physical interaction |
0.028 |
-0.017 |
|
Signal Jamming Warning |
0.019 |
-0.034 |
|
Using Locations Options to activate protection |
0.009 |
-0.028 |
|
Limit on number of connections |
0.028 |
-0.011 |
In this case, all quality indicators are calculated based on previously defined indicators. “Weights” are designated in such a way that the total for each row and column is one.
Now you can calculate the priority of each mechanism by adding the criteria score multiplied by the weight of the criteria:
The result is a table with protection mechanisms and an assessment of the priority of each of them
Mechanism priority indicators
|
Protection mechanism |
Priority indicator |
|---|---|
|
Restricting access to critical memory areas |
0.005 |
|
Data and firmware encryption |
0.004 |
|
Random number sequence generators |
0.005 |
|
Download only official firmware |
-0.0125 |
|
Dynamic pin code authentication |
0.0125 |
|
Non-Bypass Authentication Mechanisms |
-0.0005 |
|
Secure connection |
0.004 |
|
Distribution of encryption keys during pairing |
0.0065 |
|
Encryption key storage options |
-0.0075 |
|
Using the latest BLE and Bluetooth specifications |
0.0125 |
|
Restricting access to BLE services |
-0.003 |
|
Updating firmware and encryption keys |
-0.0055 |
|
Protecting the firmware update process |
-0.0055 |
|
Intrusion detection and prevention systems |
-0.0035 |
|
Machine learning algorithms for anomaly detection |
-0.0085 |
|
Anonymization of confidential data |
-0.0045 |
|
Chips with security mechanisms (Secure Element) |
-0.0085 |
|
Specialized housings and seals |
0.0065 |
|
Isolation of the BLE module from the main logic |
-0.01 |
|
External Safety Modules (HSMs) |
-0.011 |
|
Device tamper detection mechanisms |
-0.0045 |
|
Protection against electromagnetic attacks |
-0.01 |
|
Biometric authentication technologies |
0.001 |
|
Security measures at all stages of development |
-0.0045 |
|
Automatically reset or turn off the device |
-0.0015 |
|
Limiting physical interaction |
0.0055 |
|
Signal Jamming Warning |
-0.0075 |
|
Using location to activate protection |
-0.0095 |
|
Limit on number of connections |
0.0085 |
Having received all the necessary data on assessing the priority parameters of each specific protection mechanism, I sorted the mechanisms, thereby setting a strict A hierarchy of recommendations for improving the security of Internet of Things devices using BLE, which will form the basis of the security methodology.
Classification of protection mechanisms
I decided to divide the resulting list of mechanisms, distributed by priority, into 3 classes:
-
Highest priority mechanisms
-
Priority mechanisms
-
Least prioritymechanisms
In my opinion, it is impossible to call any of the mechanisms unnecessary or not recommended for implementation. This is at the very least incorrect, since any mechanism and process aimed at increasing security is definitely worth considering.
In the methodology, these classes serve as a guide for developers of Internet of Things devices using BLE technology as a communication protocol, with the help of which it will be possible to most effectively use the protection mechanisms proposed in the final qualifying work, based on the restrictions imposed by the finite set of resources and capabilities of device developers.
Based on the previously defined protection mechanisms and their priority classes, I decided to visualize the resulting hierarchy, adding recommendations for the implementation of mechanisms depending on the class in which they were determined by calculating their priority, as well as a gradient bar on the left to better understand the priority of each mechanism individually.
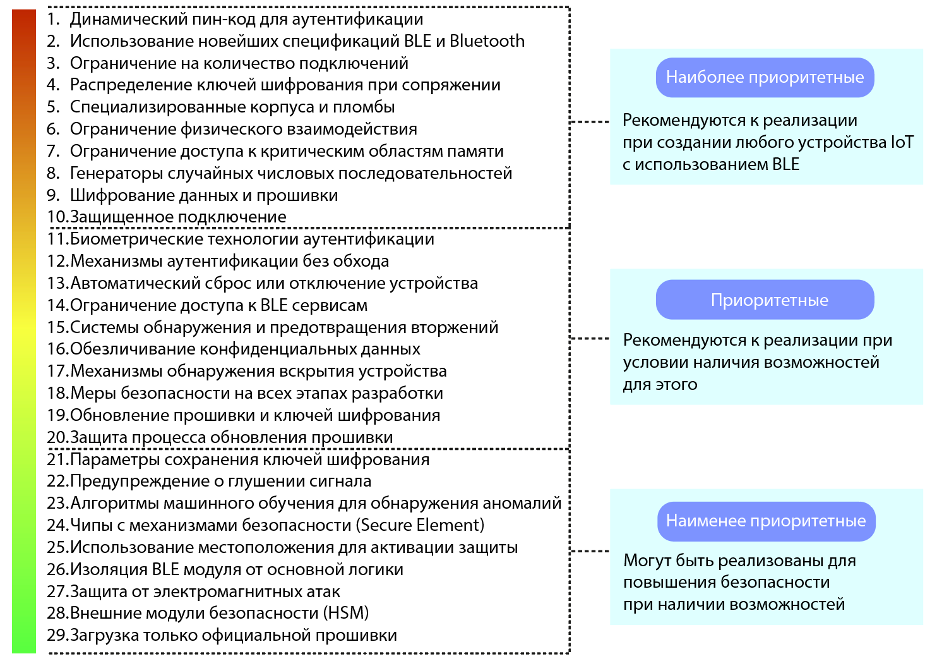
Hierarchy of IoT device protection mechanisms
This methodology can be used to guide the creation of Internet of Things devices that use BLE technology as a communication protocol in order to improve their security.
The list of protection mechanisms can be supplemented, expanded or revised if this technique is adapted to the development of other Internet of Things devices, as well as the emergence of new security threats or protection methods.
Obviously, the methodology I proposed can be further developed and updated to improve the ability to improve the security level of Internet of Things devices. In my opinion, the value of the work done, as well as the scientific novelty, lies primarily in a new approach to improving the safety of devices. In other words, it is not the resulting hierarchy itself that carries the main value (due to its incompleteness and possible erroneous judgments due to insufficient analysis and research), but the method of compiling such hierarchies based on multi-criteria selection in terms of complexity of implementation and prevention of various types of attacks.
I am confident that this method can be developed and made more accurate by introducing even more necessary indicators and criteria, which will allow us to obtain a more comprehensive and complex assessment of the priority of each individual mechanism. In any case, I am open to suggestions and discussions on this topic.
B next part This series of articles will discuss the process of creating a stationary Internet of Things device “SmartLight”.
I am grateful to everyone who took the time to read this article. It would be incredibly cool to receive feedback in the form of comments in order to improve the quality of the material.
What's next?
Since the thesis received It's quite lengthy, so I decided to break it up into several related articles:
1. Diploma of information security specialist. Part No. 1 - Methodology for ensuring the security of Internet of Things devices
2. Information Security Specialist Diploma. Part No. 2 - Stationary SmartLight device
3. Information Security Specialist Diploma. Part #3 - SmartPulse portable device
4.Information Security Specialist Diploma. Part No. 4 - Smart Connect mobile application
5. Information Security Specialist Diploma. Part #5 - Unauthorized access to IoT devices with BLEWith the original VKR can be found here
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.