Posts
🎼 Bluetooth headphones that hear more than necessary Here the news recently flashed that…
July 4, 2025 at 8:01 PM•Max Knyazev is typing…Telegram mirror
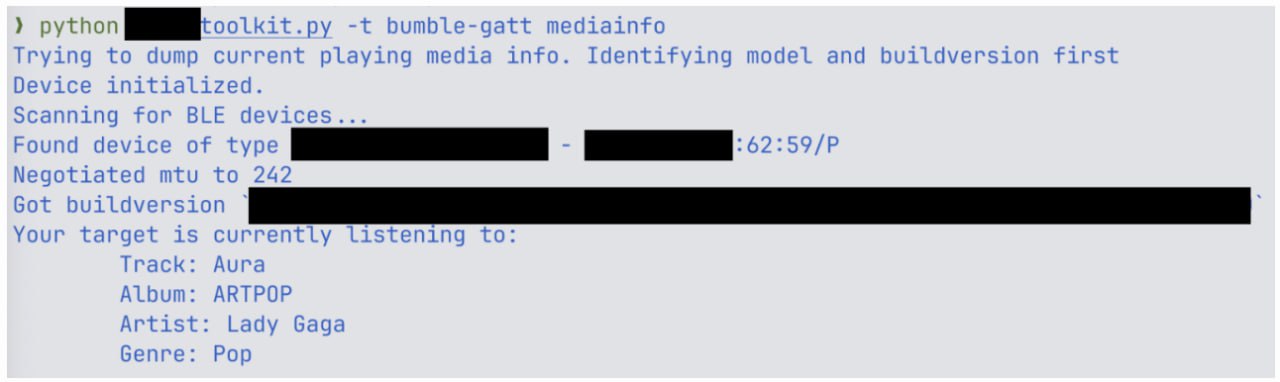
Herenewsrecently it flashed that researchers from ERNW had unearthed a whole bunch of vulnerabilities (CVE-2025-20700,CVE-2025-20701,CVE-2025-20702) in Bluetooth chip devicesAiroha. These are such popular SoCs that contain half of the TWS market from Sony and Marshall to Jabra and JBL. In fact, devices can be hacked without any connection to them, but simply by being nearby. Let's take a closer look + tell you how all this could have been avoided
The discovered vulnerabilities allow reading and writing to RAM and flash directly via Bluetooth. That is, an attacker can gain access to media content, microphone, call list and even phone contacts if the headphones are connected to it
The attack is possible via BLE GATT and Bluetooth Classic. Without confirmation and connecting to the device directly. You just need to be within a radius of 10 meters. Yes, I’ll say right away, you will need a high skill. But the result is amazing. Especially if you aim at journalists, officials, activists and celebrities, etc.
What’s especially sad is that many manufacturers don’t even know that their devices have Airoha. They simply order ready-made Bluetooth modules. And one of the vendors seems to have accidentally closed the vulnerability. By chance, Karl
The patches seem to have already been sent to manufacturers, but so far not a single device has the update. And if you're paranoid, the advice is simple: unplug your headphones from your phone and wait for updates. Well, or get out the old wired ones (PIoT security, that's what it is). The full list of vulnerable devices is given below:
Beyerdynamic Amiron 300
Bose Quiet Comfort Earbuds
EarisMax Bluetooth Auracast Sender
Jabra Elite 8 Active
JBL Endurance Race 2
JBL Live Buds 3
Jlab Epic Air Sport ANC
Marshall ACTON III
Marshall MAJOR V
Marshall MINOR IV
Marshall MOTIF II
Marshall STANMORE III
Marshall WOBURN III
MoerLabs EchoBeatz
Sony CH-720N
Sony Link Buds S
Sony ULT Wear
Sony WF-1000XM3
Sony WF-1000XM4
Sony WF-1000XM5
Sony WF-C500
Sony WF-C510-GFP
Sony WH-1000XM4
Sony WH-1000XM5
Sony WH-1000XM6
Sony WH-CH520
Sony WH-XB910N
Sony WI-C100
Teufel Tatws2
And now a few words from me
Is it even possible to make a Bluetooth device secure? In theory - yes. The protocol itself offers good security mechanisms: Secure Simple Pairing, elliptic curves, protection against MITM attacks, authenticated pairing, a white list of devices, and even the ability to require user confirmation when trying to connect.
But all this ceases to make sense if the developers on the firmware side decide: “Let’s leave the debugging interface open via BLE, without authorization, in case it comes in handy.” And this, unfortunately, is a typical scenario. The protocol itself is not to blame here. Architectural decisions are to blame when the SDK from the vendor is taken “as is”, without review and threat modeling. How many times have I already said that security is a complex thing? Well, I say it again
In the situation with Airoha, all this could have been avoided:
– By closing access to sensitive GATT services without pairing
– By disabling the debugging protocol on production builds
– By enabling encryption and authorization not only for BLE, but also for BR/EDR
– And simply by turning on the head when assembling the final firmware
But when the supply chain turns into a game of broken phone, and custom protocols live their own lives, we get this. And users, alas, as always, are the last to know
P.S. If you are developing a Bluetooth device, I beg you, think about what it will do when someone is nearby with an nRF scanner and a couple of scripts. Or, at least, do not leave open firmware on the flash drive. It's all pretty easy to read
#information_security
#internet_things
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.