Posts
If you've ever connected your phone to your car via Bluetooth and thought, “Doubtful, but…
July 24, 2025 at 8:03 PM•Max Knyazev is typing…Telegram mirror
If you've ever connected your phone to your car via Bluetooth and thought:
“Doubtful, but OKAY”
- then I have format news for you
“Not OKAY AT ALL”
. And yes, they even apply to owners
Mercedes-Benz
🚘
Researchers from PCA Cyber Security found There are four vulnerabilities in the BlueSDK Bluetooth stack from OpenSynergy, which is used in the infotainment systems of a number of cars. The attack was named Perfect Blue . It sounds like a Swiss coffee filter, but in fact it is one-touch RCE: you slip the machine into pairing - and if the user presses “OK” ( or if the automaker decided that it will do without confirmation ) - ready. Welcome to the inside of your car
🧠
Here I collected all four vulnerabilities for you:
Bugs of varying severity, but one is particularly impressive - CVE-2024-45434, use-after-free in AVRCP ( and this, for a second, is music and call management ). Further - more: after receiving the code in the context of the system, you can track GPS, eavesdrop on conversations and get into other subsystems
😅
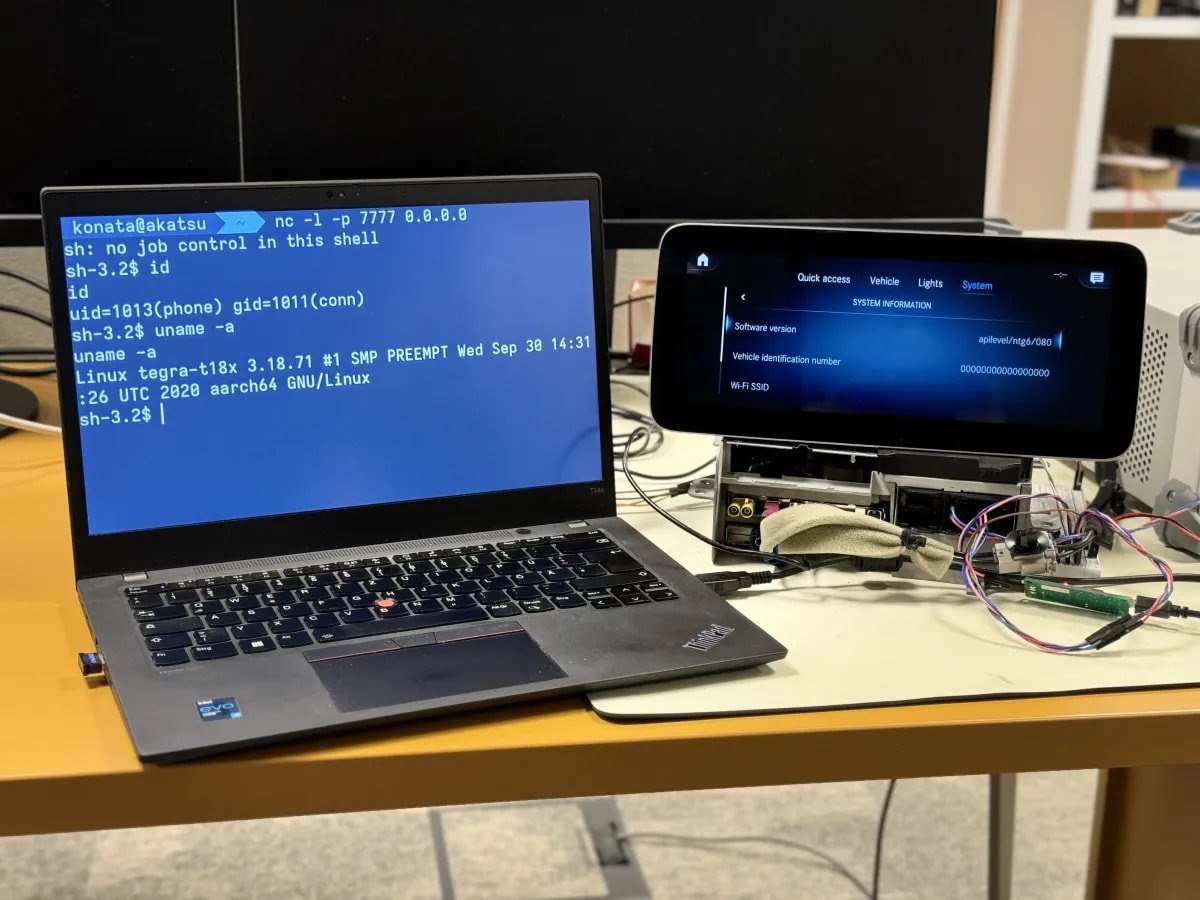
At Pwn2Own Automotive, researchers showed how you can get a reverse head unit on the head unit in a Mercedes NTG6. Over TCP/IP. From the car. Via Bluetooth. Yes, this is already the level where the entertainment ends and serious questions to vendors begin
🤬
The OpenSynergy problem was recognized back in June 2024, patches were released in September... and now, attention: according to media reports, at least one OEM was still not aware of the vulnerabilities. In 2025... I have no words
😏
Volkswagen, for example, admitted that pairing can be carried out without authorization under certain conditions. Well, at least they don’t deny it
👏
But let's look at this a little more broadly. The story with PerfectBlue is not the first and will not be the last. A few years ago, researchers Tesla was hacked via BLE , and calmly left while the owner drank coffee. Another case - exploit on Model 3 via WebKit in the car browser via Wi-Fi. Yes, Wi-Fi and Bluetooth in the car - uh is always a potential attack vector
🚗
Remember my post about hacking bluetooth headphones . Now imagine the same level of access, but in the context of a car with a CAN bus and access to coordinates, a microphone and a connection to a phone
📱
What I'm saying is that until automakers learn to think of safety not as an "afterthought" but as fundamental, stories like this will continue to repeat themselves.
🔄
#information_security
#internet_things
Open original post on TelegramResearchers from PCA Cyber Security found There are four vulnerabilities in the BlueSDK Bluetooth stack from OpenSynergy, which is used in the infotainment systems of a number of cars. The attack was named Perfect Blue . It sounds like a Swiss coffee filter, but in fact it is one-touch RCE: you slip the machine into pairing - and if the user presses “OK” ( or if the automaker decided that it will do without confirmation ) - ready. Welcome to the inside of your car
Here I collected all four vulnerabilities for you:
CVE-2024-45434 - use-after-free in the AVRCP service responsible for media control over Bluetooth
CVE-2024-45431 - Incorrect CID check in L2CAP (Logical Link Control and Adaptation Protocol)
CVE-2024-45433 – Function termination error in RFCOMM (Radio Frequency Communication) protocol
CVE-2024-45432 - Invalid parameter passing when calling RFCOMM function
Bugs of varying severity, but one is particularly impressive - CVE-2024-45434, use-after-free in AVRCP ( and this, for a second, is music and call management ). Further - more: after receiving the code in the context of the system, you can track GPS, eavesdrop on conversations and get into other subsystems
At Pwn2Own Automotive, researchers showed how you can get a reverse head unit on the head unit in a Mercedes NTG6. Over TCP/IP. From the car. Via Bluetooth. Yes, this is already the level where the entertainment ends and serious questions to vendors begin
The OpenSynergy problem was recognized back in June 2024, patches were released in September... and now, attention: according to media reports, at least one OEM was still not aware of the vulnerabilities. In 2025... I have no words
Volkswagen, for example, admitted that pairing can be carried out without authorization under certain conditions. Well, at least they don’t deny it
But let's look at this a little more broadly. The story with PerfectBlue is not the first and will not be the last. A few years ago, researchers Tesla was hacked via BLE , and calmly left while the owner drank coffee. Another case - exploit on Model 3 via WebKit in the car browser via Wi-Fi. Yes, Wi-Fi and Bluetooth in the car - uh is always a potential attack vector
Remember my post about hacking bluetooth headphones . Now imagine the same level of access, but in the context of a car with a CAN bus and access to coordinates, a microphone and a connection to a phone
What I'm saying is that until automakers learn to think of safety not as an "afterthought" but as fundamental, stories like this will continue to repeat themselves.
#information_security
#internet_things
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.