Posts
So I’m watching the second season of “The Peacemaker,” and in the fourth episode one of t…
October 13, 2025 at 7:19 PM•Max Knyazev is typing…Telegram mirror
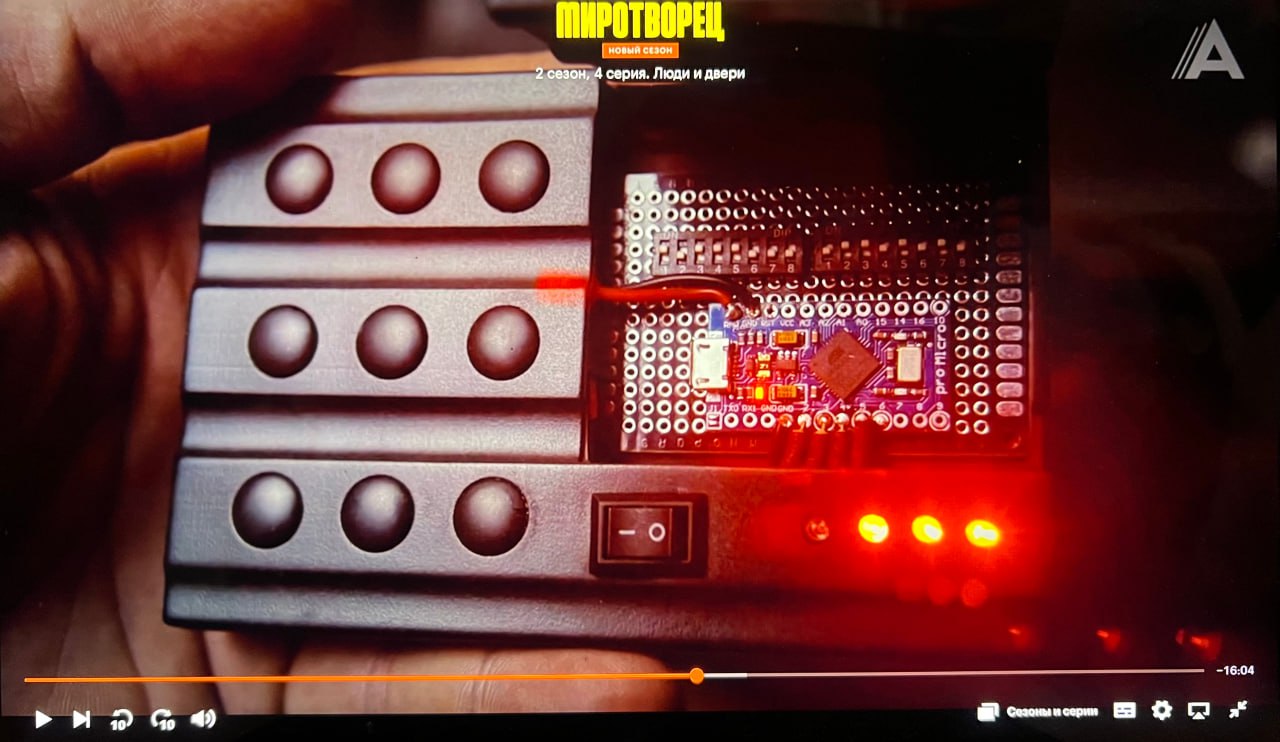
So I’m watching the second season of “The Peacemaker,” and in the fourth episode one of the main IT specialists shows his device for “hacking” combination locks on doors. And this post would not exist if the authors of the series (
hardly James Gunn personally, but still
) did not decide to show the device itself in close-up. In the frame I saw a very real device - Arduino Pro Micro based on ATmega32U4, which I myself often worked with (
as with the entire line of Arduino-like controllers
)
It is clear that it was needed only as a prop in order to believably blink the LED. And I'm not saying that anyone did the wrong thing - the props served their purpose. But you know me: I can’t just leave it like that. In this post we will figure out whether it is even possible to build a device for cracking combination locks based on Arduino Pro Micro ( without code and instructions, otherwise I'll get punished for it )
👮♂️
Brief introduction to the board ( datasheet by link ):
Most often, such microcontrollers are used for small pet projects, when they are just starting to touch embedded. The board is not capable of anything “really cool” out of the box, but, as usual, you can add different modules ( Bluetooth, Wi-Fi, etc. ), sensors, etc. That is, it is more than possible to expand its basic functionality, but the technical characteristics ( same memory ) will remain the same. Let's talk about these restrictions
🧐
16 MHz + 2.5 KB SRAM is very modest. To generate combinations ( necessary for brute force ), storing logs and complex logic will quickly exhaust resources. It is possible to write a loop that goes through all combinations, but it will be inefficient and slow. But something more complex and practical in terms of resources will not work
If the lock uses Bluetooth/Wi-Fi or proprietary radio protocols, the Pro Micro itself is useless without external modules, and these will increase complexity, size and power consumption
💯
Commercial locks are usually less than secure, but protected ( although... ): timeouts, blocking after N incorrect attempts, interface encryption and other anti-brute force mechanisms. If you go through it “blindly”, you will 100% encounter such restrictions. One more point: large-scale search benefits from the frequency of operations; The 8-bit AVR is noticeably inferior to modern 32-bit MCUs and SBCs in terms of speed and capabilities
In the end, yes On Pro Micro, you can technically implement a simple simulation of clicks and try to try very short PIN codes under ideal conditions ( no timeouts/blocking etc. ). But this is just to play around. This is not enough for us to do anything serious. The board's capabilities and resources are too limited. But now that we understand this, let's think about what kind of gadgets could theoretically be suitable for breaking combination locks (yeah, yes, recommendations on the hardware of a device for hacking - I can, I know how, I practice )
🤓
Firstly, these are all 32-bit MCUs ( RP2040/Cortex-M ). They are noticeably faster, they have more SRAM, USB Host/Device is often available and additional peripheral capabilities are very good for precise timings and more flexible logic. As one of the brightest representatives of the class, you can consider Raspberry Pi Pico
Second, SoC with radio module ( my favorite ESP32 series ): built-in Wi-Fi/Bluetooth, dual-core CPU and more memory
Well, thirdly, these are small single-board devices ( Raspberry Pi Zero-class ). You will need more energy, it will not be so compact, but you have a small laptop computer at hand. There, write and expand whatever you want and how you want. It's not even Flipper Zero, which is based on STM32. It's even better
And the series is great. I like it
🥂
P.S. Our legislation forces me to remind you: any attempts to bypass locks or enter without the explicit consent of the owner and in the absence of a legitimate research task are illegal and dangerous. I do not give instructions on how to create such devices and do not help with the exploitation of vulnerabilities in a real environment
#information_security
#internet_things
Open original post on TelegramIt is clear that it was needed only as a prop in order to believably blink the LED. And I'm not saying that anyone did the wrong thing - the props served their purpose. But you know me: I can’t just leave it like that. In this post we will figure out whether it is even possible to build a device for cracking combination locks based on Arduino Pro Micro ( without code and instructions, otherwise I'll get punished for it )
Brief introduction to the board ( datasheet by link ):
ATmega32U4 (Pro Micro) - 8-bit AVR, 16 MHz, ≈32 KB flash, ≈2.5 KB SRAM, native USB. Among the advantages, I note compactness, low power consumption, the ability to emulate USB-HID (keyboard/mouse) and simple work with GPIO
Most often, such microcontrollers are used for small pet projects, when they are just starting to touch embedded. The board is not capable of anything “really cool” out of the box, but, as usual, you can add different modules ( Bluetooth, Wi-Fi, etc. ), sensors, etc. That is, it is more than possible to expand its basic functionality, but the technical characteristics ( same memory ) will remain the same. Let's talk about these restrictions
16 MHz + 2.5 KB SRAM is very modest. To generate combinations ( necessary for brute force ), storing logs and complex logic will quickly exhaust resources. It is possible to write a loop that goes through all combinations, but it will be inefficient and slow. But something more complex and practical in terms of resources will not work
If the lock uses Bluetooth/Wi-Fi or proprietary radio protocols, the Pro Micro itself is useless without external modules, and these will increase complexity, size and power consumption
Commercial locks are usually less than secure, but protected ( although... ): timeouts, blocking after N incorrect attempts, interface encryption and other anti-brute force mechanisms. If you go through it “blindly”, you will 100% encounter such restrictions. One more point: large-scale search benefits from the frequency of operations; The 8-bit AVR is noticeably inferior to modern 32-bit MCUs and SBCs in terms of speed and capabilities
In the end, yes On Pro Micro, you can technically implement a simple simulation of clicks and try to try very short PIN codes under ideal conditions ( no timeouts/blocking etc. ). But this is just to play around. This is not enough for us to do anything serious. The board's capabilities and resources are too limited. But now that we understand this, let's think about what kind of gadgets could theoretically be suitable for breaking combination locks (yeah, yes, recommendations on the hardware of a device for hacking - I can, I know how, I practice )
Firstly, these are all 32-bit MCUs ( RP2040/Cortex-M ). They are noticeably faster, they have more SRAM, USB Host/Device is often available and additional peripheral capabilities are very good for precise timings and more flexible logic. As one of the brightest representatives of the class, you can consider Raspberry Pi Pico
Second, SoC with radio module ( my favorite ESP32 series ): built-in Wi-Fi/Bluetooth, dual-core CPU and more memory
Well, thirdly, these are small single-board devices ( Raspberry Pi Zero-class ). You will need more energy, it will not be so compact, but you have a small laptop computer at hand. There, write and expand whatever you want and how you want. It's not even Flipper Zero, which is based on STM32. It's even better
And the series is great. I like it
P.S. Our legislation forces me to remind you: any attempts to bypass locks or enter without the explicit consent of the owner and in the absence of a legitimate research task are illegal and dangerous. I do not give instructions on how to create such devices and do not help with the exploitation of vulnerabilities in a real environment
#information_security
#internet_things
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.