Posts
Based on requests from subscribers (thank you, @pleasestxpthis) ❤️❤️ On the agenda is a d…
November 25, 2024 at 5:31 PM•Max Knyazev is typing…Telegram mirror
At the request of subscribers (thank you,@pleasestxpthis)❤️ ❤️
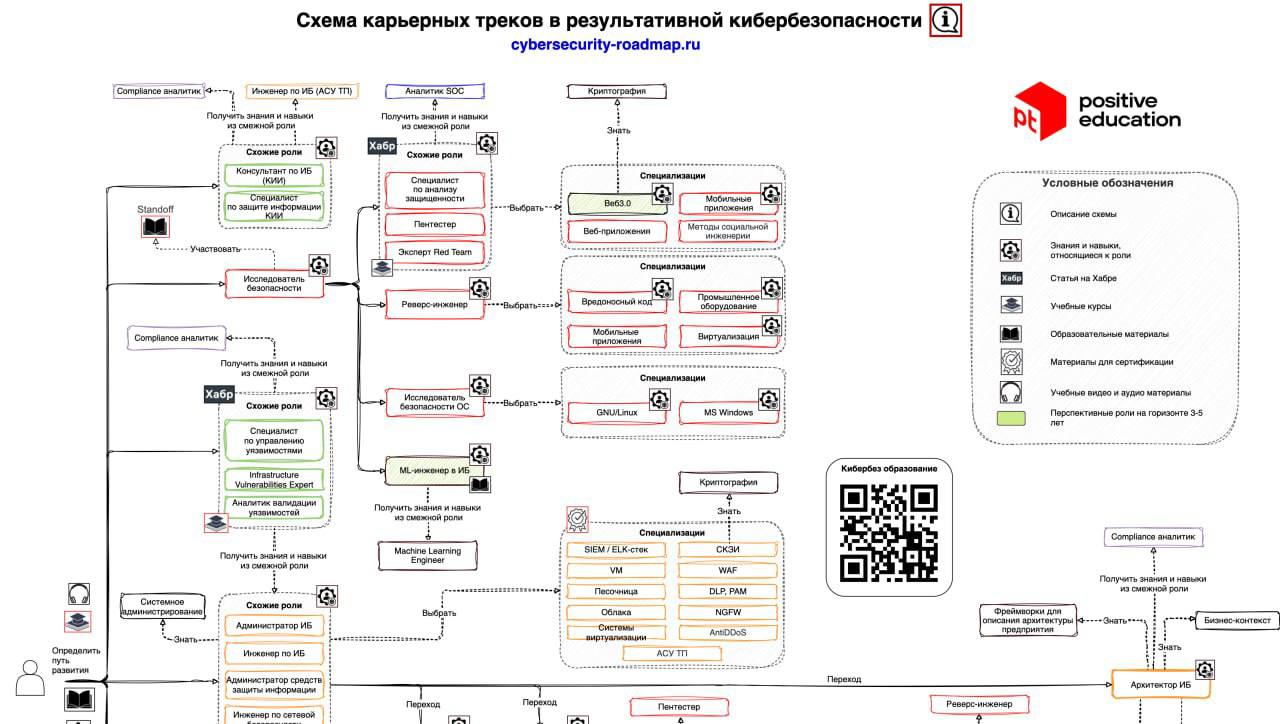
On the agendascheme of career tracks in effective cybersecurity,created by Positive Technologies specialists🤟
This is quite an impressive interactive roadmap that systematizes the main roles in the field of information security🔐
👍 The scheme covers almost all aspects of cybersecurity: from risk management and preparation of regulations to the implementation of secure software development practices and analysis of application vulnerabilities👍
As a security professional with relatively little experience (3.5 years of work + 5.5 years of university study), I can say that this is just a real find❤️ I completely agree with what PT wrote. Their recommendations are more accurate, relevant and, most importantly, applicable in practice (many tracks are described in sufficient detail). It’s a pity that during my studies at the university there was no such scheme and I had to figure out for myself “what and how it works in this information security of yours.”🤷♀️
I don’t see the point in analyzing the scheme in detail, because one post here would not be enough, and writing an article in this case is a pointless exercise. Therefore, I’ll take advantage of the situation a little and tell you about my experience + compare it with what is applicable in the scheme for me personally🚀
I started my professional development in the field of information security by working in a companySolar☀️ I came as an intern when I was in my third year at university. A year later, I was promoted to information security engineer. My range of tasks lay primarily in the field of “paper” security, but at the same time I actively used my programming skills to write tools for automating routine tasks✨
Over the course of several years of working at Solar, I managed to travel for information security audits to various government organizations and write a bunch of automation tools (which ultimately resulted in the development of a web application that is still deployed within the Solara network), and also work in the field of regulations (updating the threat and intruder model, work on certification tests, etc.)📝
But everything ends sooner or later. At some point, I realized that I wanted to go much deeper into the technical aspects and get closer to the code level, not only at the hobby level, but also at the professional level. That's how I ended up inContour❤️ as a DevSecOps engineer. Working in this direction is very different from what I did before. Now I work with secret repositories, conduct code analysis, write scripts to automate work with internal information security services and much more. As indicated in the diagram from PT, the tasks of a DevSecOps engineer have the synergy of secure development and DevOps in their foundation👨💻
If you work in cybersecurity or are simply interested in the topic, be sure to check out this framework. These are not just recommendations - this is a certain kind of action plan that will help you adjust your future professional path
↗️
#information_security
Open original post on TelegramOn the agendascheme of career tracks in effective cybersecurity,created by Positive Technologies specialists
This is quite an impressive interactive roadmap that systematizes the main roles in the field of information security
As a security professional with relatively little experience (3.5 years of work + 5.5 years of university study), I can say that this is just a real find
I don’t see the point in analyzing the scheme in detail, because one post here would not be enough, and writing an article in this case is a pointless exercise. Therefore, I’ll take advantage of the situation a little and tell you about my experience + compare it with what is applicable in the scheme for me personally
I started my professional development in the field of information security by working in a companySolar
Over the course of several years of working at Solar, I managed to travel for information security audits to various government organizations and write a bunch of automation tools (which ultimately resulted in the development of a web application that is still deployed within the Solara network), and also work in the field of regulations (updating the threat and intruder model, work on certification tests, etc.)
But everything ends sooner or later. At some point, I realized that I wanted to go much deeper into the technical aspects and get closer to the code level, not only at the hobby level, but also at the professional level. That's how I ended up inContour
If you work in cybersecurity or are simply interested in the topic, be sure to check out this framework. These are not just recommendations - this is a certain kind of action plan that will help you adjust your future professional path
#information_security
Discussion
Comments
Comments are available only to confirmed email subscribers. No separate registration or password is required: a magic link opens a comment session.
Join the discussion
Enter the same email that you already used for your site subscription. We will send you a magic link to open comments on this device.
There are no approved comments here yet.